How to Stay Away from the Spam Folder
So you moved from a free email from Yahoo or someone else to a more professional email with a domain that you own. You’re sending emails to clients and friends, newsletters to subscribers, and so forth. Everything is going smoothly. You do not want to hear from someone that your newsletter or invoice ended up in their spam folder. You also don’t want someone else to spoof your email address and send malware to someone. What do you need to do in order prevent these events from happening?
What to Do
There are two things that you to do. The first is easy, but is something that you’re going to have to constantly keep in mind. The second is technical, but if you – or someone who helped you – were able transition to a custom email, you can do this as well.
1. Don’t Send Spam
If you want to send emails to someone, there are a few things to keep in mind. Did they give you permission to send them emails? Do they know that you will be sending them newsletters? A single email or two to someone isn’t generally considered spam. But if you constantly send discount codes or product to people who don’t want to be on your email list, then that can be considered spam and treated as such. There are also other reasons why an email may be marked as spam.
Spam: unsolicited usually commercial messages (such as e-mails, text messages, or Internet postings) sent to a large number of recipients or posted in a large number of places
Merriam-Webster, 2019
If you will be sending newsletters and are located in these United States, there are requirements that you have to follow under the CAN-SPAM act of 2003. Failure to follow these requirements can lead to a fine for each email you send. It can certainly get expensive.
2. Set Up DNS Records
There are three records that you will need to have for your domain. These records are not specific to any particular email service, like G Suite or Office 365, so you don’t have to worry if that would be an issue.
- Sender Policy Framework (SPF) Record
- Domain Keys Identified Mail (DKIM) Record
- Domain-based Message Authentication, Reporting, and Conformance (DMARC) Records
Some vendors that provide hosting and email services to your may already have these records set up, but if you want to use another service to send newsletters, then you will have to add their mail servers to your records.
Quick Overview of DNS
If you already know about DNS, how it works, and how to edit DNS records, then you can skip ahead to the fun stuff here. If you don’t know much about DNS or would like a refresher, continue reading.
Websites or servers that are accessible through the internet have an IP address. For example, typing 216.58.195.78 in your web browser will take you to Google. You could remember a bunch of IP addresses for your favorite websites, but that’s just not going to happen. It’s very common for websites to have multiple IP addresses or even change addresses. It’s much easier to remember that google.com takes you to Google.
The Domain Name Server (DNS) is what allows for the internet to use words as addresses instead of numbers. You can think of DNS as a guide for you while you’re vacationing in Mexico. Let’s call him Desidro Nicolas Salinas.
You want to get to a restaurant that you saw in your travel guide, but you only know the name, “Don Hectór”, not the actual address. So you tell Desidro that you would like to go there. He finds out the address of the restaurant and takes you there.
DNS, Emails, and Spam
But that is not all that Desidro can do. Let’s suppose that you send letters from your home to other people. They also know Desidro. If he has certain information, then he will be able to do three things for them:
- Say if the return address on the letter is yours.
- Help prove that the letter came from you.
- Tell the letter recipient what to do with a letter that’s not from you.
Each of these tasks are done by a certain DNS record. SPF lists the email servers that can send emails from your domain. DKIM helps prove if a email came from the servers listed in the SPF record. Finally, DMARC lets email servers know what to do with an email claims to come from your domain, but can’t prove it. Without these records being properly set up, you have a greater chance of your emails being automatically marked as spam or someone else successfully spoofing your address. Then your emails won’t be read, because after all, who regularly checks their spam folder?
Editing DNS Records
Where you go to edit your DNS records will depend on your setup. For some setups, the domain registrar will handle the DNS records. Other setups might have the website hosting provider handle the DNS records. In any event, the entity that handles your DNS will be referred to as the provider.
Be very, very careful making changes.
Here are instructions on how to edit DNS records for some popular providers. Be sure to check the documentation for your provider before making changes.
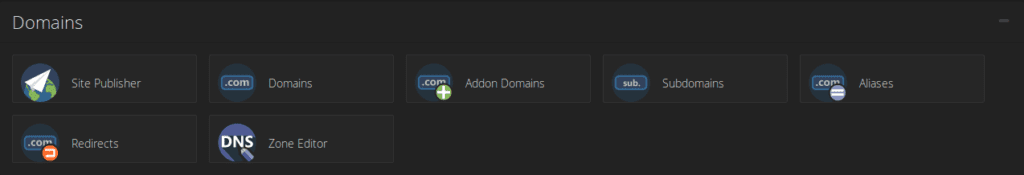
DNS records have a Name, Time to live (TTL), Type, and a Value. The records that you will be adding or changing will be text (TXT) records. These records will have certain values that makes them SPF, DKIM, and DMARC records. It’s a – all poodles are dogs, but not all dogs are poodles – situation. Your provider should have “DNS Zone” or equivalent where you can make the edits. Some providers may hide it behind “Advanced Settings”, so be sure to check their documentation if you can’t find it. You will need all three records to be effective.
Examples for Required DNS Records
Here are examples of records you will need. Be sure to check the name values of the other DNS records or your providers documentation so you can see the format your should follow. Some providers require the full domain while others allow for shorthand to be used.
| Name | Time to Live | Record |
example.com | 3600 | v=spf1 include:example.com ~all |
_domainkey.example.com | 3600 | v=DKIM1; k=rsa; p=MIG... |
_dmarc.example.com | 3600 | v=DMARC1;p=quarantine; |
The Time to Live is also important. You can think of it as the amount of time – in seconds – before a change is in effect. An hour is fine, but if your going to be making changes, you should lower the TTL to 5 minutes. That way you won’t have to wait for a day to make another change or fix a mistake.
Tools
With all the changes that you will have to make, you may want to use a few tools to help you out.
- Mail Tester rates your emails.
- SPF Record Generator generates a SPF record.
- Dmarcian checks your records.
- DMARC Weekly Digests reports what email servers are sending emails.
- DMARC Generator generates a valid DMARC record.
Sender Policy Framework (SPF) Records
What a SPF record does is help prevent spoofing. Spoofing is when other people send email from their email servers and claim that is coming from your email servers instead. The receiving servers will check if the sending servers are in the SPF record for your domain. If the sending servers are not included, then the email may be rejected or be marked as spam. This can also affect the other emails that are coming from your domain.
The name of the SPF record will be the domain name. It can be example.com or @ and will have a value like the one below.
v=spf1 include:example.com ~all| Object | Description |
v=spf1 | The SPF version being used. |
include:example.com | Server(s) that is allowed to send emails. |
~all | Only the listed servers should send emails. |
Make sure that all the domains for your email servers are there. As an example, if you are using G Suite and Mailchimp, then the record may look like this:
v=spf1 include:_spf.google.com include:servers.mcsv.net ~allHere are instructions for popular service providers. If you are using someone else, then you will have to check their documentation for their SPF configuration.
Domain Keys Identified Mail (DKIM) Records
While a SPF record says that emails must originate from certain email servers, a receiving email server will want proof. In order to check, it will look for a DKIM record.
How it works is that your email service provider generates a private and public key. The public key is used by the DKIM record. Then when you send emails, they will have a hidden signature that was generated from the private key. When a email is received, the receiving server will be able to check the signature with the public key. If the signature missing or incorrect, then the email can be rejected or marked as spam.
The name of the DKIM record follows the PREFIX._domainkey.example.com format, where PREFIX is a word that was chosen when the private and public keys were generated. Some providers will give the entire record value. It follows the format below. If the email service provider just returns the public key, then you will have to manually add the rest of the information.
v=DKIM1; k=rsa; p=MIGfMA0GCSqGSIb3DQEBAQUAA4GNADCBiQKBgQDAgq1fvkFIBjDVo4kLW8YDfGxZ94KX2feMD18nD2Qbpj0B2DRDBw1ISPLd7JBs5hFAxPTFqKGxDLkneGAk49QJ40KqXNu0mT...| Name | Description |
v=DKIM1 | Version of DKIM being used. |
k=rsa | Key type. |
p=MIG... | The public key that was generated. |
Here are instructions for popular email providers. If you’re using a someone else, then you will have to check their documentation on how to set up DKIM with their service.
Domain-based Message Authentication, Reporting, and Conformance (DMARC) Records
When a email server has a email that couldn’t prove that it came from the servers in your SPF record, the email server will want to know what it should do about that email. It will check if you have a DMARC record to see what you would like done to those emails.
There are three policies that you can use for emails that failed checks. A none policy says to let the emails to pass through. The quarantine policy says to let the emails through, but mark them as spam. As the name suggests, the reject policy says to reject those emails. The reject policy is what you want to eventually have.
However, you don’t want to set a reject policy right away is because you might have services that send newsletters or invoices from your domain. Start with a none policy that reports sent to you in order to see who is sending emails for your domain. If there are services that you want allowed, then add them to your DNS records. Make the necessary changes, then change the policy. As a safety measure, use a quarantine policy for some time before using reject.
The name of the DMARC record should follow the _dmarc.example.com format. The value for this record is what email providers refer to when they have a suspicious email. It’s best to use a tool to generate the record, which will look like the one below.
v=DMARC1;p=none;rua=mailto:admin@example.com| Name | Description |
v=DMARC1 | Version of DMARC being used. |
p=none | Which policy type to enforce. |
rua=mailto:admin@example.com | Send reports to this email. |
As mentioned before, there are three policy that you can have. All you have to change is the value of p in order to change your policy.
p=nonep=quarantinep=reject
If you would like to read more about DMARC records, here is what Google, Microsoft, and Zoho have written about them.
Summary About Staying Away from the Spam Folder
These are the steps that you need to take in order to help prevent your emails from being marked as spam. Please note that it does not guarantee that spam filters will not mark your emails as spam. Some may mark a email as spam based on its content. As a bonus, these steps will also combat people spoofing your email. It won’t stop them from trying, but it will help others catch them.
- Don’t send spam.
- Add your email servers to your SPF record.
- Generate keys for DKIM headers.
- Create a
noneDMARC policy that sends reports to you. - Add any legitimate servers to your DNS records.
- Transition to a
quarantineDMARC policy. - Make any necessary changes.
- Finish with a
rejectDMARC policy.
We also recommend that you follow the security practices that we have listed here. Even if you set up your DNS records correctly, it won’t prevent others from getting into your account and sending emails. At that point, intruders sending spam will be the least of your worries. Talk with us if you have any questions or concerns. Stay safe and secure!